The Unknown Reality: Unpacking the Next-Generation Hybrid Warfare Playbook in the Middle East
The traditional theater of war is undergoing a radical, terrifying evolution. For decades, geopolitical analysts observing the Middle East have anchored their predictions on conventional kinetic warfare—ballistic missile exchanges, naval blockades, and massive ground incursions. However, a new, comprehensive scenario analysis reveals that the next major escalation will not begin with a deafening explosion, but with a profound, engineered silence. Welcome to the era of Hybrid Warfare.
We are currently witnessing the twilight of Clausewitzian warfare as we know it. The binary concept of “war” and “peace” has been entirely dissolved by the advent of technologies that allow nation-states and non-state actors alike to operate within a perpetual “gray zone.” In this contemporary battlespace, the initial casualties are not enlisted soldiers traversing a desert landscape, but rather orbital satellites, complex trading algorithms, civilian psychology, and the foundational pillars of the global financial market. What happens when a conflict is initiated not by a declaration of war, but by a cascading failure of the systems we rely on to function as a modern society? This exhaustive analysis, based on the latest AI-driven geopolitical storyboarding and strategic wargaming, breaks down the highly probable, multi-phased escalation playbook that is currently actively rewriting regional power dynamics in the Middle East.
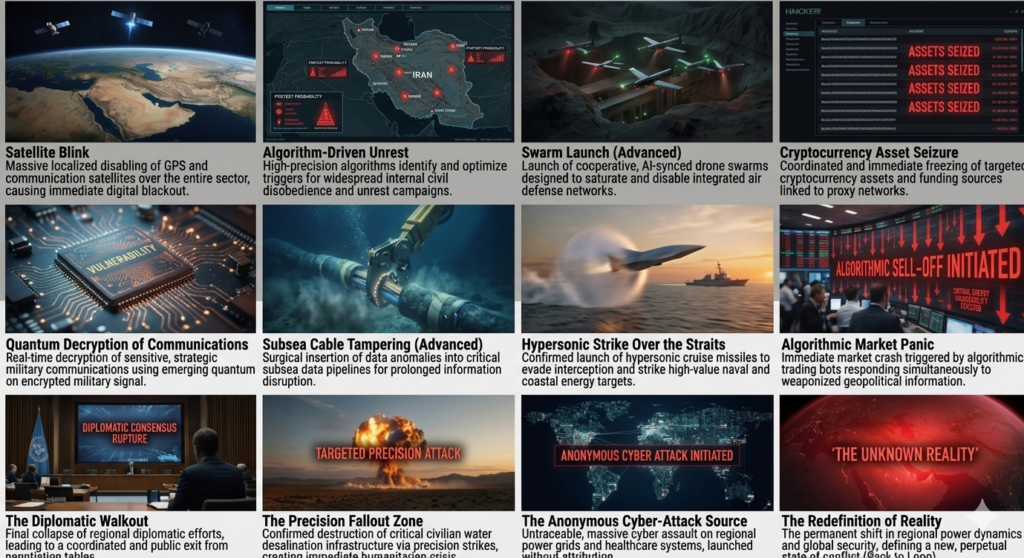
Phase I: The Digital Blinding and Asymmetric Disruption
Before a single physical shot is fired, the modern battlefield must be plunged into absolute darkness. The objective of the opening gambit in a 21st-century conflict is total information denial and the systematic dismantling of the adversary’s situational awareness. You cannot fight what you cannot see, and you cannot command forces you cannot communicate with.
The Orbital Blackout: The Weaponization of Space
The conflict initiates with what strategists term a “Satellite Blink.” Massive, localized disabling of GPS and communication satellites over the entire Middle Eastern sector causes an immediate, catastrophic digital blackout. Modern military infrastructure is fundamentally dependent on space-based assets. From the precision guidance systems of smart munitions to the secure communication links connecting naval carrier strike groups to central command, orbital infrastructure is the Achilles’ heel of modern superpowers.
This blackout would likely be achieved not through spectacular kinetic missile strikes against satellites (which would create undeniable debris fields and invoke immediate Article 5-style retaliations), but through sophisticated Electronic Warfare (EW) and localized jamming. Directed energy weapons (DEWs) or rogue satellite proximity operations (where “sleeper” satellites drift close to critical military satellites) can scramble signals or permanently blind optical sensors without creating space debris. The immediate result on the ground is chaos: civilian logistics halt, commercial aviation is grounded, and state-of-the-art military hardware is suddenly reduced to 1970s-era operational capabilities.
Algorithmic Unrest: Cognitive Warfare on the Homefront
Simultaneous to the blinding of the military, the adversary launches a devastating offensive against the civilian population. This is not done with bombs, but with code. Concurrently, high-precision algorithms are deployed to identify and optimize triggers for widespread internal civil disobedience. By weaponizing social media, deepfakes, and existing domestic fault lines, state actors force their adversaries to fight a two-front war—one external, one deeply internal.
We have moved beyond simple bot farms spreading misinformation. Next-generation cognitive warfare utilizes Large Language Models (LLMs) and advanced AI to hyper-personalize propaganda at scale. These systems identify psychological vulnerabilities in specific demographics within a target nation. They can generate thousands of unique, highly convincing narratives—complete with AI-generated video and audio—designed to incite panic, spark sectarian violence, or erode public trust in the government’s ability to handle the escalating crisis. Imagine millions of citizens receiving spoofed alerts regarding contaminated water supplies or imminent financial collapse, perfectly timed to coincide with actual, minor disruptions. The goal is to collapse the state from within, exhausting internal security forces before foreign boots ever approach the border.
The Cyber & Quantum Offensive: The Death of Encryption
The silent strike continues with an untraceable, massive cyber assault on regional power grids, water purification plants, and healthcare systems. The legacy of malware like Stuxnet has evolved into highly autonomous, self-propagating zero-day exploits that can lay dormant in critical infrastructure networks for years, waiting for a single execution command.
More alarmingly, we are on the precipice of “Q-Day”—the moment when emerging quantum computing capabilities can successfully break standard RSA encryption. In our advanced scenario, the adversary utilizes early-stage quantum decryption to expose encrypted military communications in real-time. This effectively neutralizes strategic secrecy. Command directives, troop movements, and nuclear posture communications are intercepted and read as plain text. The psychological impact of a military realizing its most secure communications are entirely compromised cannot be overstated; it leads to strategic paralysis.
“In modern hybrid warfare, the most devastating weapon is not the one that destroys a city, but the one that makes the city tear itself apart while its defenders watch, blind and deaf, incapable of communication.” — Strategic Defense Initiative Wargame Report, 2025.
Phase II: Economic Strangulation and Infrastructure Sabotage
Warfare has fully integrated with the globalized, hyper-connected economy. The second phase of the playbook weaponizes financial interconnectivity to cripple the adversary’s ability to sustain prolonged conflict. In a war of attrition, the victor is the one who can outlast the economic hemorrhage.
Algorithmic Market Panic: The Weaponization of Wall Street
Information—both real, fabricated, and selectively delayed—is fed directly to the high-frequency trading (HFT) bots that control the vast majority of global stock market volume. By coordinating minor physical attacks (such as a localized fire at a minor oil facility) with a massive, AI-driven dissemination of catastrophic rumors across financial terminals, an adversary can trigger an immediate, algorithmic market crash.
This orchestrated financial panic drains national reserves, plummets the value of fiat currencies, and spooks foreign investment within a matter of hours. The economic damage inflicted by a manufactured “Flash Crash” can exceed the cost of a physical bombing campaign, wiping out billions in sovereign wealth and civilian pensions. By manipulating the global perception of energy security in the Middle East, an attacker essentially taxes the entire world, leveraging global economic anxiety to force international pressure onto the target nation to capitulate.
Proxy Asset Seizure: The Shadow War of Cryptocurrencies
In the shadows of the decentralized finance (DeFi) boom, proxy networks, militias, and non-state actors rely heavily on digital ledgers for untraceable funding. The modern hybrid warfare playbook includes the coordinated and immediate freezing of targeted cryptocurrency assets.
While blockchain is theoretically decentralized, the entry and exit points (exchanges) and the underlying infrastructure (mining pools, server farms) are highly vulnerable to state-level cyber operations. Advanced intelligence agencies now possess blockchain forensics capabilities that can trace the flow of illicit funds through “mixers” and “tumblers.” In an escalation scenario, a sudden, massive cyber-operation would permanently lock the wallets of proxy forces, paralyzing the logistical supply chains of mercenary groups and proxy armies. Without the ability to pay fighters or purchase black-market munitions, the adversary’s asymmetric ground advantage evaporates instantly.
Subsea Severance: Cutting the Global Nervous System
Far beneath the ocean surface lies the physical reality of the “cloud.” Over 95% of all global communications and massive daily financial transactions travel through a network of armored subsea fiber-optic cables. The Middle East, particularly the Red Sea and the Persian Gulf, serves as one of the world’s most critical subsea data chokepoints.
In Phase II, specialized autonomous underwater vehicles (AUVs)—indistinguishable from civilian oceanic research drones—are deployed. Their mission is the surgical insertion of data anomalies into critical subsea data pipelines, or, in a severe escalation, the physical severing of these cables. Cutting just three specific cables in the Red Sea region can isolate entire nations from the global internet. The economic cost of a target nation losing internet connectivity is devastating. It halts digital banking, grounds maritime shipping reliant on digital manifests, and creates an information vacuum that state-sponsored cognitive warfare campaigns (as described in Phase I) can quickly fill.
Phase III: The Lethal Kinetic Pivot
Only after the adversary is deaf, blind, economically paralyzed, and dealing with widespread internal riots does the conflict transition to the kinetic realm. However, these are not the symmetrical dogfights or tank battles of the 20th century; this is the deployment of next-generation autonomous lethality. The goal is maximum strategic impact with minimum risk of prolonged engagement.
AI-Synced Drone Swarms: The Saturation Strategy
Traditional integrated air defense systems (IADS), such as the Patriot missile system or the Iron Dome, were designed to track and intercept distinct, high-value, fast-moving targets like fighter jets or ballistic missiles. They are economically and technologically ill-equipped to handle the weaponization of biomimicry.
The kinetic phase begins with the launch of cooperative, AI-synced drone swarms. Hundreds, or even thousands, of cheap, 3D-printed loitering munitions are launched from disguised shipping containers or underground silos. These drones do not rely on central command; they use localized mesh networks and artificial intelligence to communicate with each other like a flock of birds. If one drone is destroyed, the swarm instantly recalculates its flight path and attack vectors.
The strategy here is “saturation.” The swarm is designed to intentionally absorb multi-million-dollar interceptor missiles, rapidly depleting the target’s defensive magazines. A $2,000 drone forces the firing of a $3 million interceptor—a cost-exchange ratio that will bankrupt a defending military in days. Once the defensive magazines are empty, the remaining drones surgically dive-bomb critical radar installations, permanently blinding the target nation to what comes next.
Hypersonic Dominance: The Unstoppable Strike
With the skies cleared and early-warning radars reduced to smoking craters, the definitive physical blow is delivered. The confirmed launch of hypersonic glide vehicles (HGVs) or hypersonic cruise missiles fundamentally alters the physics of warfare. Traveling at speeds exceeding Mach 5 (over 3,800 mph), these weapons do not follow a predictable parabolic ballistic trajectory. They glide along the upper atmosphere, capable of extreme, unpredictable maneuvering.
Because they fly lower than traditional ballistic missiles but faster than cruise missiles, they remain hidden from ground-based radar by the curvature of the earth until the very last moments of flight. By the time they are detected, impact is seconds away. Hypersonic weapons allow for the surgical striking of high-value naval assets (such as aircraft carriers, rendering traditional power projection obsolete) and coastal energy infrastructure. A successful hypersonic strike on a major oil export terminal in the Strait of Hormuz would not only cripple the target’s export economy but send global energy markets into a catastrophic, unrecoverable spiral.
Precision Infrastructure Targeting: The Humanitarian Leverage
The final physical phase shifts from strictly military targets to the targeting of critical civilian lifelines. In arid regions like the Middle East, water is a strategic vulnerability. The confirmed destruction of massive water desalination infrastructure via precision strikes—or via the cyber operations initiated in Phase I—creates an immediate, terrifying humanitarian crisis.
By depriving millions of citizens of potable water, the attacking force generates unbearable domestic pressure on the target government to surrender. This tactic leverages human suffering as a strategic weapon, forcing international humanitarian organizations to intervene and fundamentally altering the diplomatic landscape. The target state must divert its remaining military logistics to simply keeping its population alive, effectively ending its capacity to wage external war.
Phase IV: Diplomatic Fallout and The Redefinition of Reality
The culmination of these staggering, rapid-fire events leads to a complete rupture in international diplomatic consensus. Institutions like the United Nations, built to mediate conflicts between conventional standing armies, find themselves entirely paralyzed. How do you pass a Security Council resolution against a cyberattack that cannot be definitively attributed? How do you sanction a drone swarm with no national insignia? The legal frameworks of the Geneva Conventions are stretched to breaking point by the realities of hybrid warfare.
As regional diplomatic efforts collapse, we witness a coordinated and public exit from negotiation tables. Ambassadors are recalled not due to policy disagreements, but because the very infrastructure of their host nations is collapsing around them. The targeted nation, completely isolated digitally, economically, and physically, is left to navigate a dystopian reality.
What emerges from this scenario is not a traditional post-war peace treaty signed on the deck of a battleship. Instead, it is a perpetual state of “un-peace”—a permanent shift in regional power dynamics and global security. The victor has proven that a nation can be systematically dismantled without the attacking force ever crossing a physical border. This creates a terrifying precedent, establishing a new global arms race focused not on nuclear warheads, but on quantum computing, artificial intelligence, and cyber-offensive capabilities.
Conclusion: Preparing for the Invisible War
This “Unknown Reality” dictates a hard truth: the wars of tomorrow will be fought everywhere and nowhere simultaneously. The battlefield is no longer a defined geographic location; it is the internet cable under the ocean, the code running the stock exchange, the satellite orbiting the earth, and the psychological resilience of the civilian population.
For policymakers, defense strategists, and citizens alike, the question is no longer if this hybrid playbook will be executed. The technologies required for every phase of this scenario already exist and are actively being refined by state actors across the globe. The only remaining question is who holds the technological supremacy, the cybersecurity infrastructure, and the societal resilience to survive it when the silent war finally begins.